- HOME
- ABOUT US
- SERVICES
Information Technology & Application Services
- INDUSTRIES
- JOBS
- Resume
- Blog
- CONTACT US
- DIGITAL
APIs have quietly become the backbone of the digital economy.
From mobile apps and SaaS platforms to cloud services, fintech systems, and enterprise integrations — everything runs on APIs. In fact, modern enterprises now expose hundreds or even thousands of APIs across internal systems, partners, and customers.
But this rapid expansion has created a critical problem.
APIs are now the most targeted attack surface in modern applications.
As we enter 2026, API security is no longer a niche technical concern — it is a business-critical security priority. Organizations that fail to protect their APIs risk data breaches, service outages, compliance violations, and loss of customer trust.
APIs power:
More APIs mean more entry points for attackers.
Unlike traditional web apps, APIs often provide:
A single vulnerable API can expose millions of records.
APIs:
As a result, API abuse is increasing faster than any other attack type.
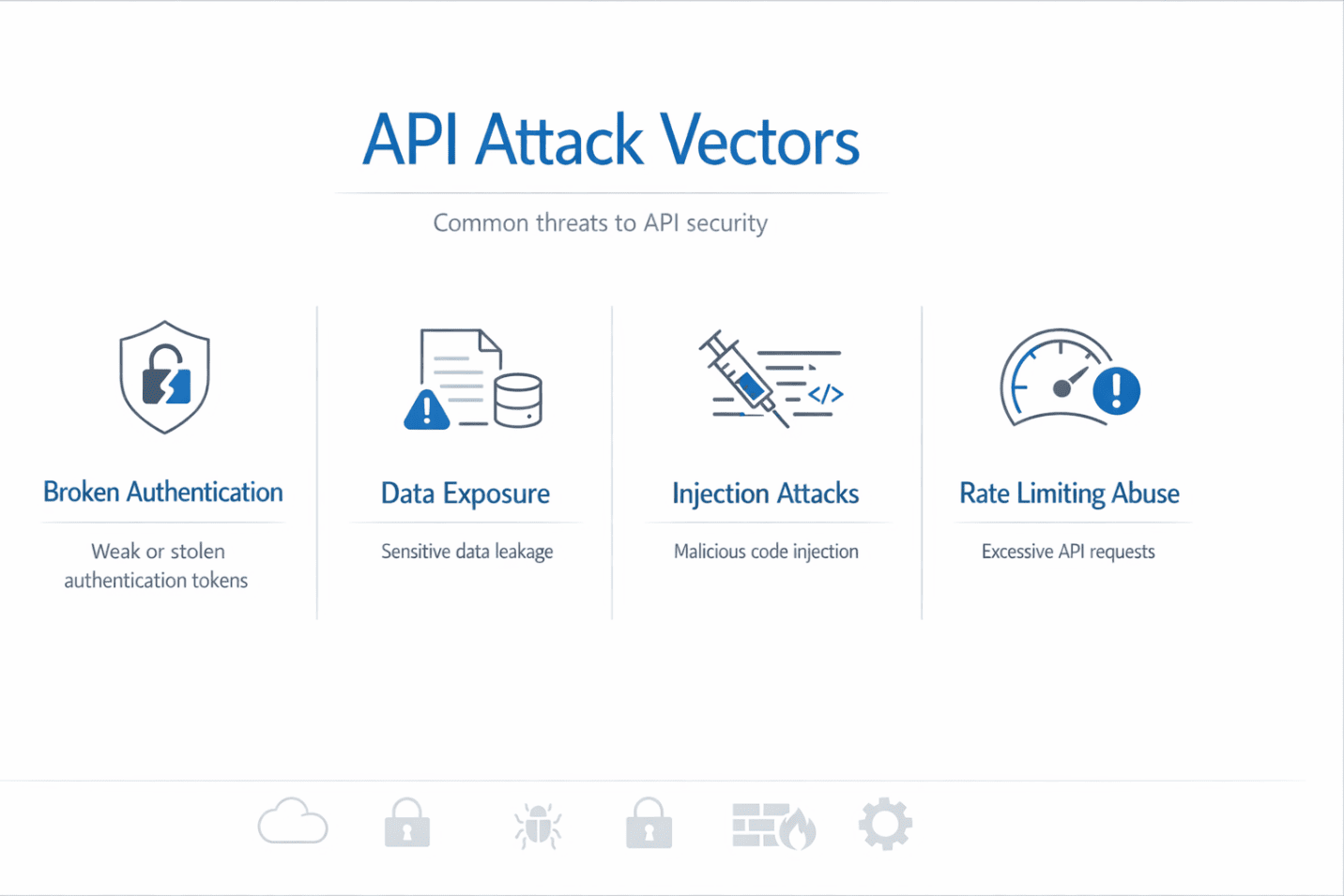
Threat | Impact |
Broken authentication | Account takeover |
Excessive data exposure | Data breaches |
Injection attacks | System compromise |
Rate-limit abuse | Denial of service |
Shadow APIs | Unknown attack surface |
Weak authorization | Privilege escalation |
Industry reports show that API-related breaches now account for a majority of modern application attacks.
These tools were designed for web traffic, not modern API behavior.
Without API-specific controls, attacks go unnoticed until damage is done.
Every API request must be:
No API should trust internal traffic by default.
APIs should expose only what is necessary, nothing more.
Prevent:
Real-time visibility into:
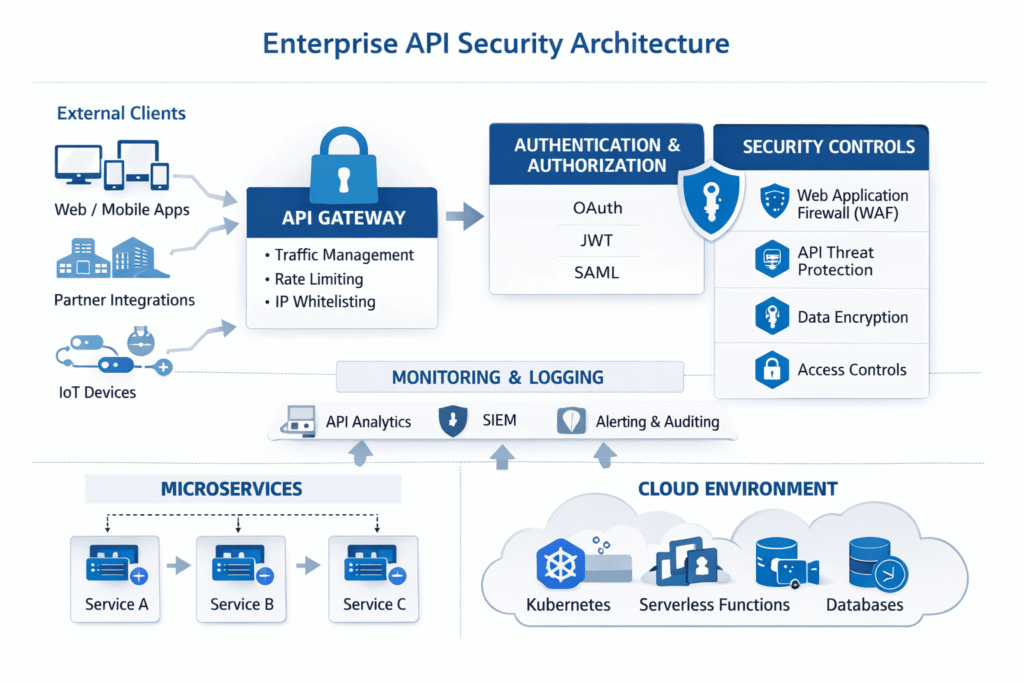
APIs play a critical role in regulatory compliance, including:
Unsecured APIs often lead to:
Strong API governance is now essential for compliance readiness.
✔ Maintain a complete API inventory
✔ Secure APIs by design, not after deployment
✔ Enforce authentication on every endpoint
✔ Validate input and output data
✔ Monitor APIs continuously
✔ Test APIs regularly for vulnerabilities
✔ Retire unused and shadow APIs
API security must be embedded into the development lifecycle, not added later.
Organizations that treat APIs as first-class security assets will operate with confidence in an interconnected digital ecosystem.

APIs are the foundation of modern digital business — and the most vulnerable link in the security chain.
In 2026, protecting APIs is no longer optional. It is essential for safeguarding data, ensuring compliance, and maintaining customer trust.
At JPS Tech Solutions, we help enterprises design, secure, and govern APIs across cloud and hybrid environments — ensuring innovation without compromise.
👉 Ready to strengthen your API security strategy? Talk to our experts today.
