
- HOME
- ABOUT US
- SERVICES
Information Technology & Application Services
- INDUSTRIES
- JOBS
- Resume
- Blog
- CONTACT US
- DIGITAL
Cybersecurity in 2025 isn’t just about building walls — it’s about assuming that the walls are already breached.
With digital ecosystems expanding across cloud platforms, mobile devices, and remote users, the traditional “castle-and-moat” security model no longer holds up.
A single weak link — a phishing email, an unpatched API, or a compromised employee credential — can bring down entire systems.
That’s where Zero Trust Architecture (ZTA) steps in: a model that assumes no user or device is trustworthy by default, no matter where it operates.
In 2025, cyber threats are evolving faster than ever:
According to Cybersecurity Ventures, global cybercrime costs are expected to reach $10.5 trillion annually by 2025 — making cybersecurity the single largest business risk of the digital era.
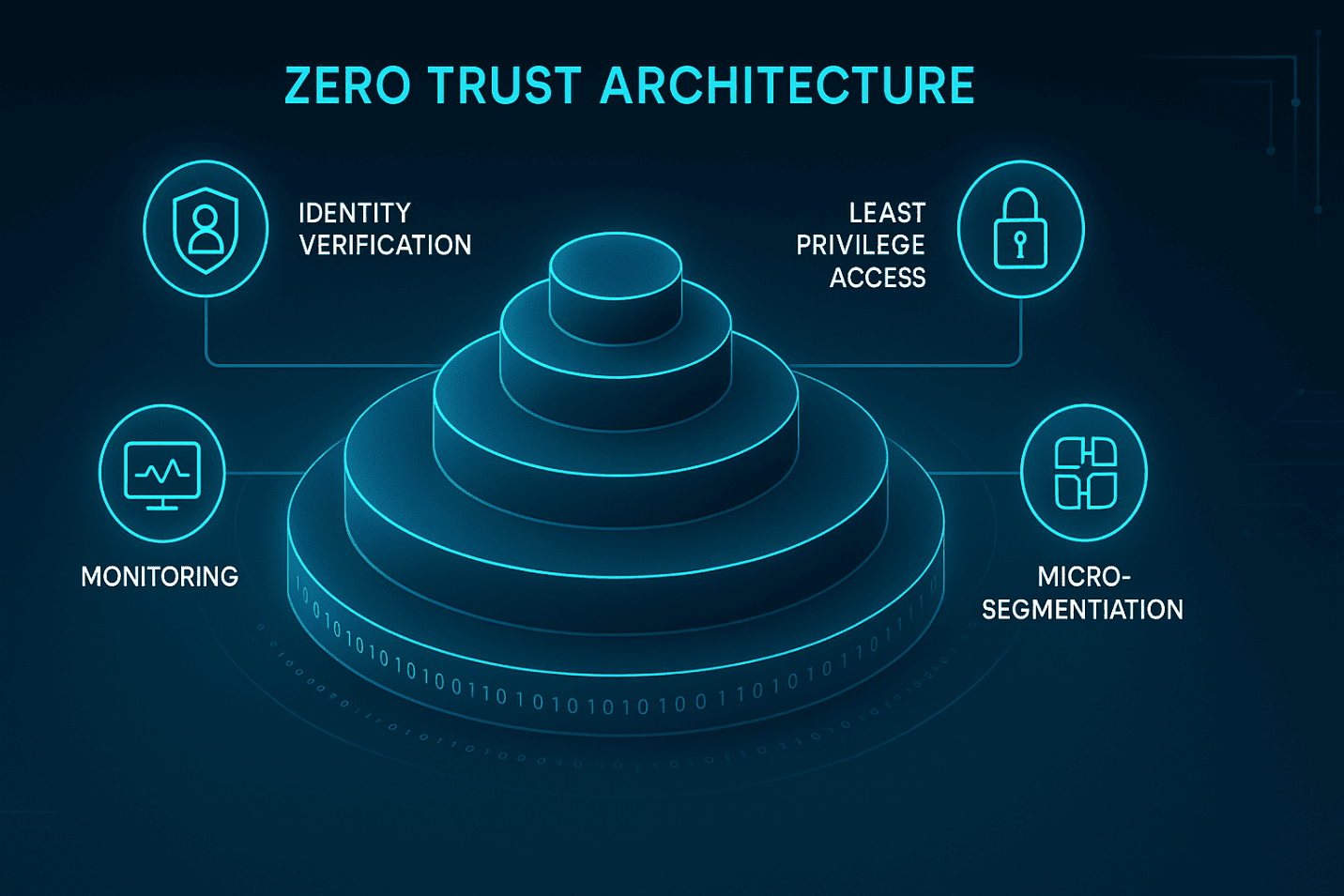
Zero Trust is built on a simple principle: “Never trust, always verify.”
Instead of granting access based on network location, Zero Trust continuously validates every user, device, and transaction.
1. Identity Verification – Multi-factor authentication and continuous identity checks.
2. Least Privilege Access – Users only get access to the data they need.
3. Micro-Segmentation – Dividing networks into smaller, secure zones.
4️. Continuous Monitoring – Real-time analytics and behavioral anomaly detection.
5. Data Encryption Everywhere – Securing data at rest, in transit, and in use.
With multi-cloud and hybrid setups, perimeters no longer exist. Zero Trust provides the dynamic, identity-based controls needed to secure these environments.
Employees log in from homes, coffee shops, and airports. Zero Trust validates every session — wherever it originates.
Laws like GDPR, CCPA, and India’s DPDP Act demand stronger data protection. Zero Trust aligns perfectly with these frameworks.
AI security tools rely on clean, verified data streams. Zero Trust ensures that data pipelines remain uncompromised.
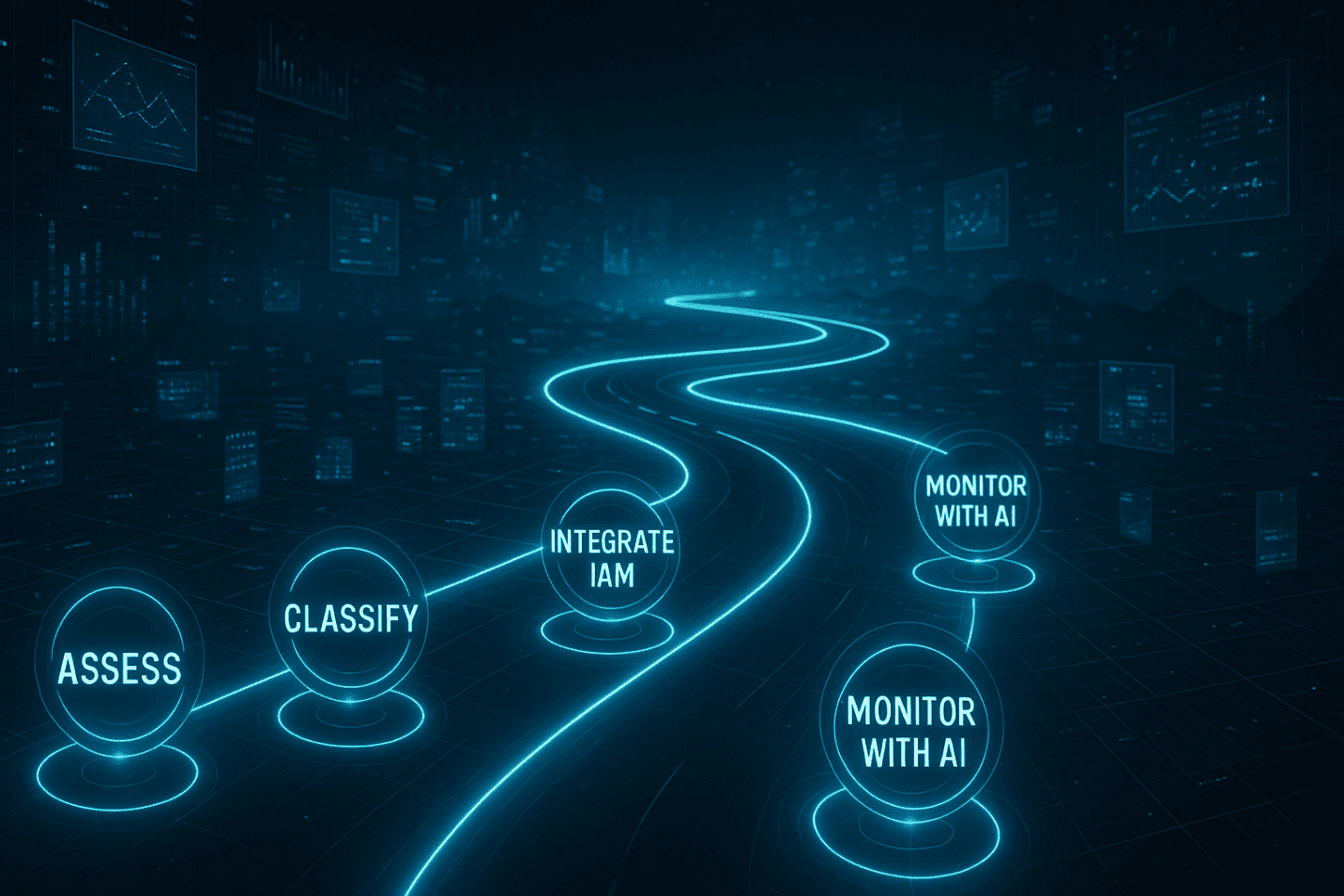
Adopting Zero Trust is a journey, not a switch.
Start with clear visibility into your digital assets, then build security in layers.
1️. Assess your current security posture.
2️. Classify critical data and access roles.
3️. Integrate identity management (IAM) and MFA.
4️. Use network micro-segmentation and endpoint verification.
5️. Adopt AI-driven monitoring and threat detection tools.
✅ Reduced risk of data breaches
✅ Improved visibility and control
✅ Regulatory compliance and audit readiness
✅ Enhanced customer trust and brand reputation
📊 Companies adopting Zero Trust report up to 40% fewer security incidents within the first year, according to Gartner.
However, with expert partners and phased execution, these obstacles can be overcome efficiently.
By 2026 and beyond, Zero Trust will evolve with AI integration, quantum-resistant encryption, and real-time adaptive security models.
The future belongs to proactive defenders — not reactive responders.

Cybersecurity in 2025 demands more than firewalls — it demands Zero Trust thinking.
In a world where breaches are inevitable, trust must be earned, verified, and constantly monitored
At JPS Tech Solutions, we help enterprises build Zero Trust frameworks tailored to their cloud, data, and compliance environments — transforming security from a checkpoint into a continuous business enabler.
👉 Ready to reimagine your business for the future? Talk to our experts today.
© Copyright 2026 – JPS Tech Solutions. All Rights Reserved.